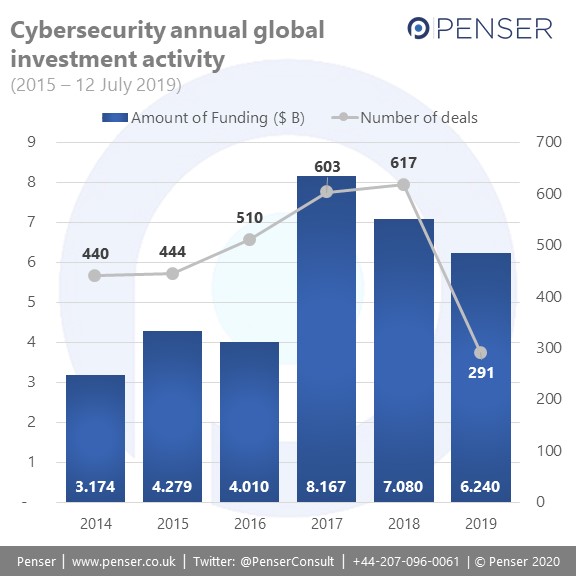
Cybersecurity, as an industry, is booming. Spending on cybersecurity is on track to surpass $133 billion in 2022 and the market has grown over 30x in 13 years. This is likely driven by both the sophisticated level of cyber attacks by bad actors, as well as the large number of data breaches reported over the last decade. Investments in cybersecurity start-ups is rising, and CB Insights has reported that there are now 13 cybersecurity companies that have entered the ‘unicorn club’, i.e. companies that are currently valued at over $1 billion.
- Tanium: Tanium offers a platform for endpoint management and security, allowing its customers to secure all connected devices in their enterprise.
Total Disclosed Funding: $770.3 M
Current Valuation: $6.6 B - Qi An Xin: Qi An Xin provides big data, content, endpoint, and perimeter security for customers in government, enterprises, and more.
Total Disclosed Funding: $864.3 M
Current Valuation: $2.5 B - Cloudflare: Cloudflare sends its customers’ web traffic through its own global network, allowing it to optimize performance and page load time, while providing protection against a variety of cyber-attacks.
Total Disclosed Funding: $332.1 M
Current Valuation: $1.8 B - Kaseya: The Kaseya platform provides monitoring, management, security, and continuity.
Total Disclosed Funding: $550 M
Current Valuation: $1.8 B - Darktrace: Darktrace is working to manage risk from cyber-attacks by using AI to detect abnormal behaviour in organisations.
Total Disclosed Funding: $232.3 M
Current Valuation: $1.7 B - Lookout: Lookout helps its customers secure mobile devices against app, device, and network-level threats. Lookout can help protect users from viruses, can backup and restore data, and locate lost or stolen phones.
Total Disclosed Funding: $281 M
Current Valuation: $1.3 B - 4Paradigm: 4Paradigm allows enterprises to detect fraud, improve efficiency, reduce risk, and market to customers. The platform uses AI to analyse online customer habits and is mainly marketed toward financial services firms.
Total Disclosed Funding: $145 M
Current Valuation: $1.2 B - Illumio: Illumio helps organizations overcome data centre and cloud security challenges by preventing the spread of cyber threats with micro-segmentation, real-time application dependency mapping, and more.
Total Disclosed Funding: $332.2 M
Current Valuation: $1 B - Tongdun Technologies: Tongdun Technologies provides anti-theft and anti-fraud risk control services. By using big data, AI, and cloud computing, Tongdun hopes to establish an intelligent anti-fraud decision-making platform.
Total Disclosed Funding: $236.4 M
Current Valuation: $1 B - Netskope: Netskope offers a platform for companies to protect against threats to data in cloud applications and cloud infrastructure, allowing IT to direct usage, protect sensitive data, and ensure compliance in real-time on any device.
Total Disclosed Funding: $400.1 M
Current Valuation: $1 B - Auth0: Auth0 offers a secure login system for companies to authenticate the identity of employees for web, mobile, IoT, and internal applications.
Total Disclosed Funding: $212.2 M
Current Valuation: $1 B - KnowBe4: KnowBe4 is helping companies manage the problem of social engineering tactics by training users to recognize red flags via tools that enable IT to send simulated phishing emails to users.
Total Disclosed Funding: $393.2 M
Current Valuation: $1 B - Druva: Druva is a SaaS company that delivers cloud data management and protection built on AWS.
Total Disclosed Funding: $328 M
Current Valuation: $1 B
With cybercrime getting more sophisticated, a new breed of cybersecurity players is emerging on the scene to ensure data is housed securely. These new players – named “Cyber Defenders” by CB Insights – are approaching cybersecurity issues armed with cutting-edge technology and innovative techniques. We take a closer look at the approaches adopted, and highlight some of the start-ups making an impact in that subcategory.
- Cyber Patrols
As most (if not all) devices, infrastructure, apps and more are now connected to the internet, the number of potential entry points that could be exploited by bad actors has increased manifold. These Cyber Patrols scan the internet for rogue servers and endpoints, ensuring that the risks associated with assets connected to the internet are better managed.
KEY START-UPS –- Expanse: An automated global internet intelligence company, Expanse offers real-time detection and classification of connected digital assets and the risks they pose to organizations.
- Censys: Censys analyses real-time internet data of every connected device, and is used by researchers, corporations and governments.
- Deepfake Detection
Deepfakes are a synthetic media that involves replacing a person in an existing image or video with someone else’s likeness. Using a machine learning technique called a Generative Adversarial Network, deepfakes can manipulate or generate audio/visual content with a high potential to deceive. Start-ups are now using AI, cryptography and other technologies to authenticate media and help spot high-quality fakes.
KEY START-UPS –- Truepic: TruePic is an online image and video authenticity provider. They authenticate media by verifying their origin, pixel contents, and metadata at capture. The unique cryptographic signature of media captured using TruePic’s app is written to the blockchain, creating an immutable record.
- AI Foundation: AI Foundation develops tools for fighting digital deceptions by combining human moderation and machine learning. The software runs while browsing the web, similar to a virus protection system, scanning media encountered for fakes.
- Crypto Forensics
As cryptocurrency provides avenues for bad actors to cover the origin and receipt of funds, they are often used to launder dirty money and fund illegal activities. Start-ups have stepped in to aid law enforcement institutions in tracking and identifying the sources and destinations of cryptocurrency transactions.
KEY START-UPS –- CipherTrace: CipherTrace develops cryptocurrency anti-money laundering, forensics, and blockchain threat intelligence solutions.
- Chainanalysis: Chainanalysis specializes in enhanced due diligence for tracing the flow of funds for specific transactions and more, and sells crypto compliance and investigation software.
- Homomorphic Encryption
Data exists at three states in in the enterprise life cycle – data at rest, data in transit and data in use. Traditional encryption is able to secure data at rest and in transit, but have found challenges in finding effective solutions for securing data in use. As a result, actions, such as search, analytics, etc., have required decryption, creating vulnerable points that could be exploited. Homomorphic encryption lets enterprises operate on sensitive encrypted data without decrypting it, which could have far-reaching impacts on how data is managed.
KEY START-UPS –- Enveil: Enveil is an innovative date security company looking to make homomorphic encryption commercially viable.
- Fortanix: Fortanix offers run time encryption which enables applications to process and work with encrypted data in public clouds.
- Democratized Encryption
Democratized encryption is about providing enterprise-grade encryption and surveillance-free communication to all.
KEY START-UPS –- Signal Foundation: The Signal Foundation is a non-profit focusing on developing open source privacy technology to enable access to secure global communications.
- Tresorit: Tresorit is a cryptographically secure cloud storage service designed for small-and medium-size enterprises that need compliance, security, and confidentiality.
- Secure Firmware
Firmware is software that provides the low-level control for a device’s hardware functionality. Start-ups are looking to provide solutions that secure firmware from cyber-attacks.
KEY START-UPS –- ReFirm Labs: The company offers enterprises the ability to automatically vet, validate, and monitor firmware security in connected devices.
- Eclypsium: Eclypsium fights firmware, hardware and supply chain attacks. Eclypsium specializes in gaining full visibility into an organization’s devices and their underlying hardware components.
- Anonymous Analytics
Start-ups are creating solutions that anonymise data thereby offering privacy, reduced risk of data breaches, while still allowing enterprises to derive insights from personal data.
KEY START-UPS- Privitar: The company offers a mix of privacy tech, governance, and data management for enterprises to safely derive insights from PII.
- Hazy: Hazy develops tech that automates synthetic data creation, and works with financial clients that conducts fraud investigations and generates risk models.
- National Cybersecurity
Start-ups are working on addressing nation-state directed attacks and ways to classify unknown and evasive types of malware.
KEY START-UPS –- ReversingLabs: ReversingLabs fights advanced threats and polymorphic malware, and works with antivirus vendors, security vendors, government agencies, and commercial enterprises.
- Claroty: Claroty’s platform helps protect critical industrial control systems. The company specializes in visibility into the A range of ICS, SCADA, and other control devices, protocols, and OT networks.
- Botnet Force Shields
Botnets are armies of networked infected devices that simultaneously attack and overwhelm sites and online businesses. Using AI, some start-ups are able to analyse incoming traffic and flag potentially malicious activity in real-time.
KEY START-UPS –- PerimeterX: PerimeterX uses AI and behavioural fingerprinting technologies (technologies designed to analyse and distinguish between normal and anomalous behaviour that may be generated by an automated tool) to detect and defend websites from various types of botnet attacks.
- Signal Sciences: Signal Sciences is a DevOps security company where the platform is deployed in the development environment so as to aid developers in the creation of secure web applications.
- Infosec Education
Start-ups are using online courses and gamification techniques to enhance the cyber skills of users and potentially develop qualified cybersecurity personnel.
KEY START-UPS –- Immersive Labs: Immersive Labs offers cyber training labs on demand. Courses are streamed, gamified, and offer multiple disciplines, such as secure coding, ethical hacking, etc.
- Cybrary: An online cyber classroom and professional network, Cybrary provides free cyber training classes.
- Armoured Email
Email remains an extremely vulnerable point of exposure. Aside from phishing scams, more sophisticated email scams are also on the rise, such as whaling, misdirected emails, and man-in-the-middle scams.
KEY START-UPS –- Tessian: Tessian specialises in analysing security threats in emails through the use of AI and machine-learning to analyse historical email data and identify potential threats early.
- Virtru: Virtru offers an email encryption and data privacy platform that gives enterprises control over who receives, reviews and retains sensitive data.
- Cloud-native Security
Startups are rising to help secure cloud computing with solutions that increase network visibility and control through container visibility, vulnerability management and micro-segmentation.
KEY START-UPS –- StackRox: StackRox helps DevOps teams map container environments from services to applications and monitor for vulnerabilities.
- Portshift: Portshift helps enterprises deploy, manage, and secure application workloads by infusing security into DevOps.
- Secure Programming
Secure Programming is focused on setting up platforms for securing code from production to runtime, especially for mission critical software.
KEY START-UPS –- Tangram Flex: Tangram Flex secures mission critical software used for defence.
- Secure Code Warrior: Secure Code Warrior offers interactive learning scenarios that enable developers to master cybersecurity coding techniques.
- Attack Simulators
Enterprises are shifting from passive defence to active defence. Start-ups are now providing solutions that simulate cyberattacks to proactively identify vulnerabilities and gaps in the security infrastructure.
KEY START-UPS –- Synack: Synack offers crowdsourced cybersecurity penetration testing by scanning the organisation’s network and raising alerts when vulnerabilities are identified.
- XM Cyber: XM Cyber provides an automated cyber threat simulator that applies AI to automatically simulate system exploits and vulnerabilities.
Cybersecurity is becoming increasingly more important as lines are blurred between traditional and digital businesses. Nowhere is this more prevalent than in the fintech space, where legacy players are looking to revamp their services in order to provide innovative solutions that their customers are looking for. These new-age ‘cyber defenders’ are looking to provide tech-driven solutions to deal with increasingly sophisticated cyberattacks.
As fintech consultants, we are committed to ensuring that we offer our clients the most relevant and up-to-date information on key developments in the industry. Through our technical due diligence services, we help clients identify vulnerabilities and gaps in the business’s IT infrastructure, and often recommend solutions that are on the cutting-edge. Our commercial due diligence services also provide clear, comprehensive reports that outline the strengths and weaknesses of the target company.
If you’d like to learn more about our due diligence services, request a sample report by clicking here.
We also provide consulting services in strategic planning and digital transformation. Find out more by visiting our services page.